Enable data collection for Check Point devices
Relevant for: AFA Administrators
Note: In addition the requirements listed below, ensure that the user that AFA is using to access the device has the required permissions. The minimum permission required in Read Only All. When the device is using ActiveChange, the minimum permission is Read Write All. For more details, see Required device permissions.
For more details, see Add Check Point devices.
In this topic:
Enable data collection via SSH
This procedure describes how to enable AFA to process Check Point application control traffic logs.
AFA can be configured to collect logs from a Check Point device via SSH, but special configuration is required on the Check Point device. Application control traffic logs include the app_rule_id field, and this field is masked by default for the SSH log collection user that is specified when adding the device to AFA. As a result, AFA cannot process application control logs that are collected via SSH, nor use them to generate information for the Application Control Rules Cleanup area of the device report's Policy Optimization page.
In order to enable AFA to process application control traffic logs, you must modify permissions for the app_rule_id field on the Check Point device, as described in the following procedure.
Note: For R80 and above, AFA collects data via REST (along with either SSH or OPSEC). For more details, see Enable data collection via REST.
Do the following:
-
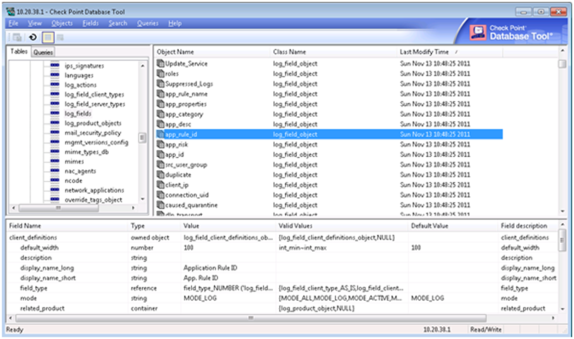
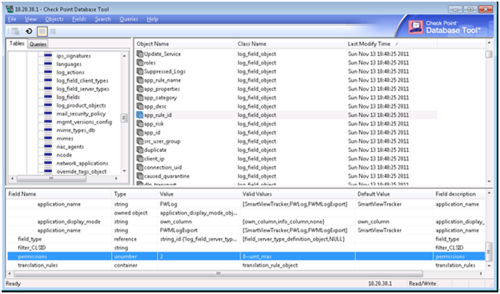
Run GuiDBedit.exe, and connect to the Check Point device's management station.
The management station is typically located at C:\Program Files (x86)\CheckPoint\SmartConsole\RXX\PROGRAM
where RXX is the version number.
-
In the left pane, navigate to Other > log_fields.
-
In the right pane, click on app_rule_id.
The bottom pane displays the fields that are displayed for app_rule_id.
-
In the bottom pane, double-click on the permissions field.
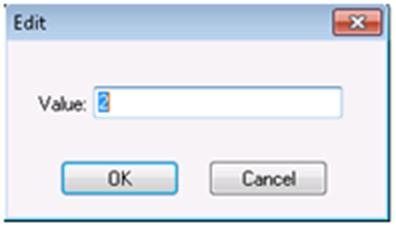
The Edit dialog is displayed.
- In the Value field, change the value from 2 to 0.
- Click OK.
- Save your changes and exit the program.
-
If the device sends its traffic logs to a log server other than the management station (for example, a CLM or external log server), do the following:
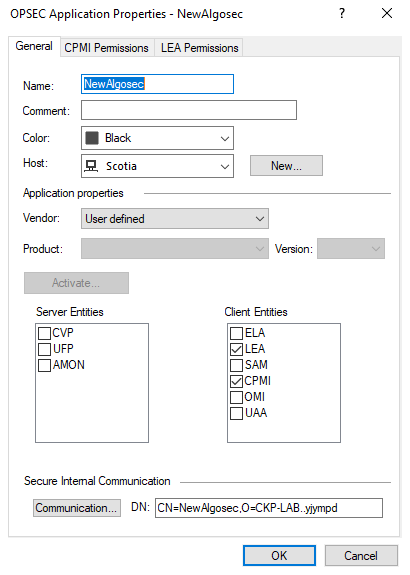
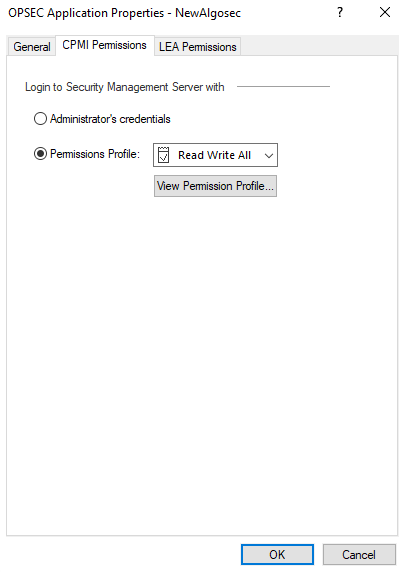
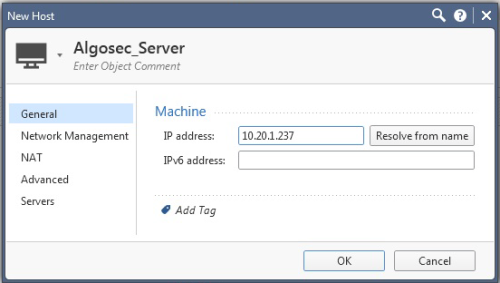
Enable data collection via OPSEC
This procedure describes how to specify a certificate for OPSEC access to a Check Point device, which must be performed in the Check Point - Multi-Domain Security Management (Provider-1) - Step 1/3 or Check Point - SmartCenter or CMA - Step 1/2 page after selecting OPSEC as the connection method.
Do the following:
-
Create a certificate for your device. For more details, see:
-
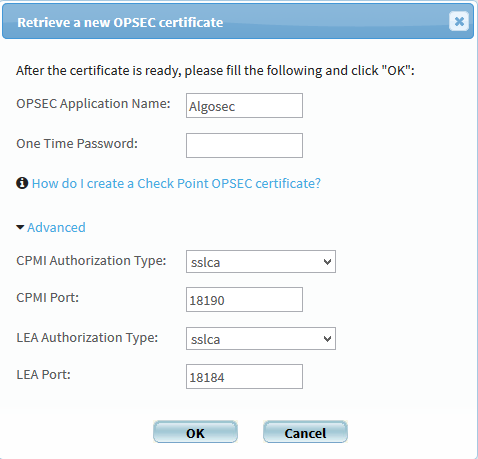
In AFA, in the OPSEC Setup area, click Certificate.
The Retrieve a new OPSEC certificate dialog is displayed.
-
Complete the fields as follows:
OPSEC Application Name
Type the OPSEC application name, as specified in the OPSEC certificate.
The default value is "AlgoSec".
One Time Password
Type the one-time password, as specified in the OPSEC certificate.
Advanced
Click to display advanced fields.
The CPMI Authorization Type, CPMI Port, LEA Authorization Type, and LEA Port fields appear.
CPMI Authorization Type
Select the CPMI authorization type.
CPMI Port
Type the CPMI port number.
The default value is 18190.
LEA Authorization Type
Select the LEA authorization type.
LEA Port
Type the LEA port number.
The default value is 18184.
-
Click OK to retrieve the certificate from the Check Point SmartCenter, CMA or MDSM server.
Once the certificate is installed, a confirmation window appears.
-
Click OK.
The OPSEC Setup area displays the certificate date and time of creation.
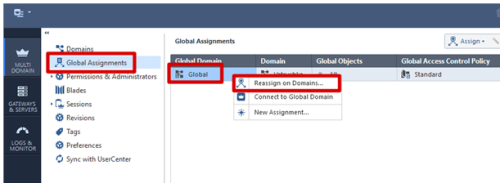
Enable data collection via REST
This procedure describes how to enable REST calls to the Security Management Server.
Note: For versions R80 and above, AFA collects data via REST, along with either SSH or OPSEC. In addition to enabling REST, you must also enable SSH or OPSEC as needed.
For details, see Enable data collection via SSH and Enable data collection via OPSEC.
Do the following:
-
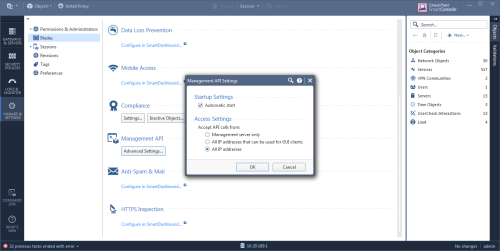
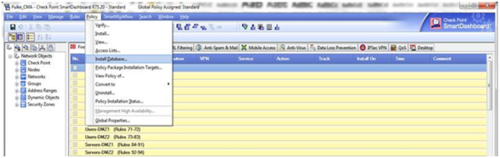
Open a SmartConsole.
-
In the left pane, navigate to Manage & Settings > Blades > Management API > Advanced Settings.
The Management API Settings window appears.
- To automatically start the API server at Security Management Server startup, select the Automatic Start check box.
-
Select which IP addresses from which the API server accepts requests:
All IP addresses that can be used for GUI clients API server will accept scripts and web service requests from the same devices that are allowed access to the Security Management Server. Make sure the AFA server is in this list. All IP addresses The API server will accept scripts and web-service requests from any device -
Click OK.
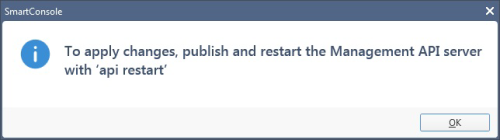
In the Management API restart message that appears, click OK.
- At the top, click Publish.
- In the Management Check Point Server CLI, run the api restart command, and then exit.

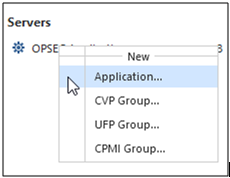

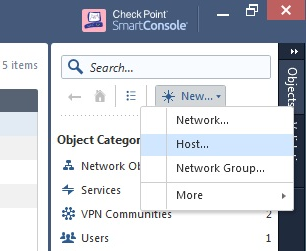
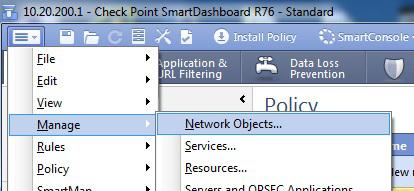
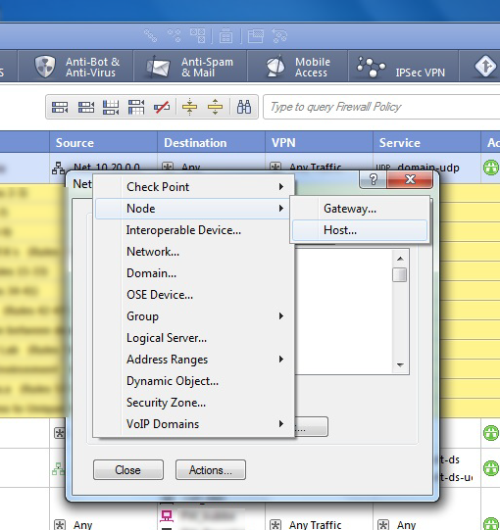
 icon at the top left of the screen and select:
icon at the top left of the screen and select: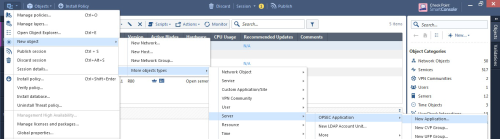
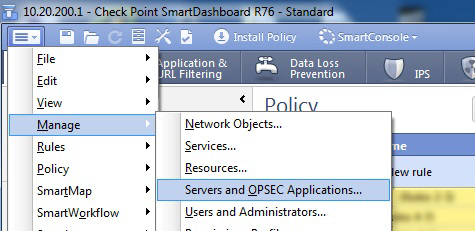
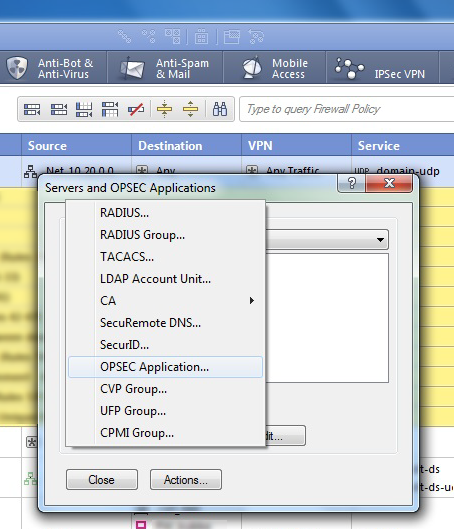
 icon, and select
icon, and select