IPv6 traffic change workflow
This topic describes the events that occur in each stage in a default iPv6 traffic change workflow.
This type of traffic change is supported only for Cisco devices.
Note: FireFlow is fully configurable, and your system may differ.
In this topic:
Request
- The requestor selects a template on which to base their request.
- If the template specifies a workflow, FireFlow assigns the request to that workflow.
-
The requestor submits the request to FireFlow.
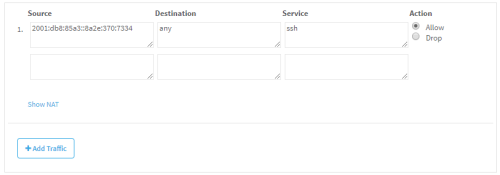
The request may include information about the relevant source, destination, service, and action for the change. For example, the requestor may submit the following request:
- FireFlow receives the request information and creates a change request.
- If a workflow has not yet been assigned, FireFlow assigns a workflow. For more details, see Request templates and workflows.
- The default assignee of the role handling new change requests (by default, the Network Operations role) is assigned as the change request's owner.
- FireFlow sends an email message informing the requestor that the change request was created, and specifying the change request ID in the format [FireFlow #<number>], for example [FireFlow #49].
Plan
In the Plan stage, a user with a network operations role plots out the technical changes needed in order to satisfy the change request. This stage consists of the following steps:
-
The change request may change ownership in one of the following ways:
- The change request owner assigns it to a user with the network operations role.
- A network operations user chooses to take responsibility for the change request.
- The network operations user confirms the devices that are relevant to the requested change.
- The network operation user sends the change request on to the next stage.
- If the network operations user selected multiple devices, FireFlow generates a sub-request for each.
Approve
In the Approve stage, a user with the information security role determines the security risks entailed in satisfying the request. This stage consists of the following steps:
- The default assignee of the role handling change requests in the Approve stage (by default, the Information Security role) is assigned as the change request's owner.
-
The change request may change ownership in one of the following ways:
- The change request owner assigns it to a user with information security role.
- An information security user chooses to take responsibility for the change request.
-
The information security user does one of the following:
- Approves the change request and sends it on to the next stage.
- Rejects the change request and returns it to the Plan stage.
- Rejects and closes the change request. In this case, an email message is sent to the requestor, indicating that the request is denied.
- Contacts the requestor and asks for more information.
Implement
In the Implement stage, the network operations user plans and executes request implementation.
This stage consists of the following steps:
- The change request's ownership is returned to the network operations user.
- FireFlow creates a work order and displays a list of recommendations for implementing the requested change.
- The network operations user edits the list of recommendations and adds notes to the work order.
- The network operations user manually implements the requested changes on the devices according to the work order.
- The network operation user sends the change request on to the next stage.
Validate
In the Validate stage, the requestor checks that the request was implemented, and the network operations user resolves the change request. This stage consists of the following steps:
- The network operations user composes an email message in FireFlow, notifying the requestor that the requested changes were implemented.
- FireFlow sends the email to the requestor.
- The requestor checks that the requested change was implemented and the desired result was achieved.
-
One of the following things happens:
- If the desired result was not achieved, the requestor responds via an email message or via the Web interface, and the network operations user then re-initiates the implementation stage.
- If the desired result was achieved, the requestor responds via email message or via the Web interface, and the network operations user then resolves the change request.
- If the requestor does not respond, the network operations user can choose to resolve the change request anyway.
At this point, the change request's lifecycle has effectively ended, and no further user action is required. However, the change request remains available in the system for auditing purposes, as described in the final stages.
Resolved
Once the change request has been validated, it enters the Resolved stage.
Audit
The Audit stage for IPv6 traffic change request lifecycles is identical to the Audit stage for traffic change request lifecycles. See Audit.